Calling all Regex/Splunk wizzes
Discussion
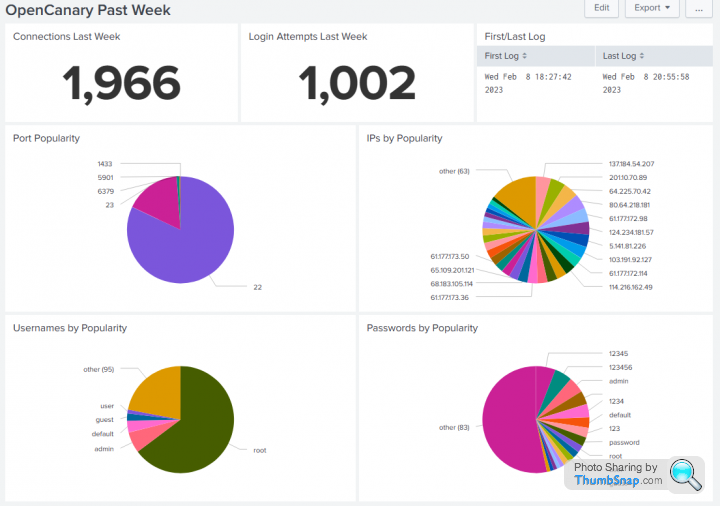
I have an OpenCanary on the Internet and am sending events into Splunk. That works a treat.
Now I want to extract fields from the darn thing but it's not happy, mostly because the fields occur at different locations in the log lines.
Fields I want are Port (dst_port - which works because it does not get punted around location-wise), Username, Password and SourceIP (src_host). It's all nicely structured but my Regex skills are not great and are coming up short.
Can anyone help? Naturally, I want Password to be after the PASSWORD\": but ^(?:.*"PASSWORD\":\s*")(?P<Password>\w+\!@#\d+) is not working for me in Splunk. Free virtual beers for anyone who can assist
message="{\"dst_host\": \"10.0.0.117\", \"dst_port\": 23, \"local_time\": \"2023-02-08 16:20:12.113362\", \"local_time_adjusted\": \"2023-02-08 17:20:12.113390\", \"logdata\": {\"PASSWORD\": \"admin\", \"USERNAME\": \"Administrator\"}, \"logtype\": 6001, \"node_id\": \"hostname.domain\", \"src_host\": \"114.216.162.49\", \"src_port\": 47106, \"utc_time\": \"2023-02-08 16:20:12.113383\"}" path=/opencanary/A _SECRET full_path=/opencanary/A
_SECRET full_path=/opencanary/A _SECRET query="" command=POST client_address=100.86.224.114 client_port=54770
_SECRET query="" command=POST client_address=100.86.224.114 client_port=54770
message="{\"dst_host\": \"10.0.0.117\", \"dst_port\": 22, \"local_time\": \"2023-02-08 16:20:11.922514\", \"local_time_adjusted\": \"2023-02-08 17:20:11.922544\", \"logdata\": {\"LOCALVERSION\": \"SSH-2.0-OpenSSH_5.1p1 Debian-4\", \"PASSWORD\": \"abc123!\", \"REMOTEVERSION\": \"SSH-2.0-PUTTY\", \"USERNAME\": \"root\"}, \"logtype\": 4002, \"node_id\": \"hostname.domain\", \"src_host\": \"61.177.172.124\", \"src_port\": 17802, \"utc_time\": \"2023-02-08 16:20:11.922536\"}" path=/opencanary/A _SECRET full_path=/opencanary/A
_SECRET full_path=/opencanary/A _SECRET query="" command=POST client_address=100.86.224.114 client_port=54768
_SECRET query="" command=POST client_address=100.86.224.114 client_port=54768
Now I want to extract fields from the darn thing but it's not happy, mostly because the fields occur at different locations in the log lines.
Fields I want are Port (dst_port - which works because it does not get punted around location-wise), Username, Password and SourceIP (src_host). It's all nicely structured but my Regex skills are not great and are coming up short.
Can anyone help? Naturally, I want Password to be after the PASSWORD\": but ^(?:.*"PASSWORD\":\s*")(?P<Password>\w+\!@#\d+) is not working for me in Splunk. Free virtual beers for anyone who can assist

message="{\"dst_host\": \"10.0.0.117\", \"dst_port\": 23, \"local_time\": \"2023-02-08 16:20:12.113362\", \"local_time_adjusted\": \"2023-02-08 17:20:12.113390\", \"logdata\": {\"PASSWORD\": \"admin\", \"USERNAME\": \"Administrator\"}, \"logtype\": 6001, \"node_id\": \"hostname.domain\", \"src_host\": \"114.216.162.49\", \"src_port\": 47106, \"utc_time\": \"2023-02-08 16:20:12.113383\"}" path=/opencanary/A
 _SECRET full_path=/opencanary/A
_SECRET full_path=/opencanary/A _SECRET query="" command=POST client_address=100.86.224.114 client_port=54770
_SECRET query="" command=POST client_address=100.86.224.114 client_port=54770message="{\"dst_host\": \"10.0.0.117\", \"dst_port\": 22, \"local_time\": \"2023-02-08 16:20:11.922514\", \"local_time_adjusted\": \"2023-02-08 17:20:11.922544\", \"logdata\": {\"LOCALVERSION\": \"SSH-2.0-OpenSSH_5.1p1 Debian-4\", \"PASSWORD\": \"abc123!\", \"REMOTEVERSION\": \"SSH-2.0-PUTTY\", \"USERNAME\": \"root\"}, \"logtype\": 4002, \"node_id\": \"hostname.domain\", \"src_host\": \"61.177.172.124\", \"src_port\": 17802, \"utc_time\": \"2023-02-08 16:20:11.922536\"}" path=/opencanary/A
 _SECRET full_path=/opencanary/A
_SECRET full_path=/opencanary/A _SECRET query="" command=POST client_address=100.86.224.114 client_port=54768
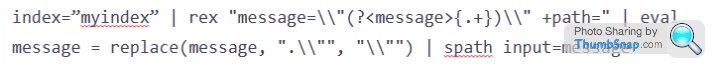
_SECRET query="" command=POST client_address=100.86.224.114 client_port=54768I tend to grab things like this and stick into a new field:
index=* | rex field=_raw "<leading_search> (?<new_field_name><regex>)"
To return the password in a field called "pwd", I'd use something like this:
However, I can't quite work out if you posted the "raw" message, so you might have to fiddle with the location of the special characters, which you'll ave to escape first.
HTH
M
index=* | rex field=_raw "<leading_search> (?<new_field_name><regex>)"
To return the password in a field called "pwd", I'd use something like this:
index=* | rex field=_raw "PASSWORD\": \"(?<pwd>\s+\)"
However, I can't quite work out if you posted the "raw" message, so you might have to fiddle with the location of the special characters, which you'll ave to escape first.
HTH
M
Gassing Station | Computers, Gadgets & Stuff | Top of Page | What's New | My Stuff